Account Data Review – 18332925853, Transappgo, сапиоснксуал, Redandwhitemagz .Com, здфекгь
The account data review for 18332925853 and associated entities maps transactional history, usage patterns, and identity linkages to observable activities and relationships within a defined footprint. It emphasizes data minimization, privacy-by-design, and governance clarity, while outlining boundaries and accountability. Red flags—weak consent, inconsistent minimization, unclear retention, and fragmented accountability—signal gaps that demand cross-functional controls and ongoing audits. Stakeholders must assess risk, define flows, and implement improvements to regain regulatory alignment, leaving implications for next steps to consider.
What Account Data Really Means for 18332925853 and Friends
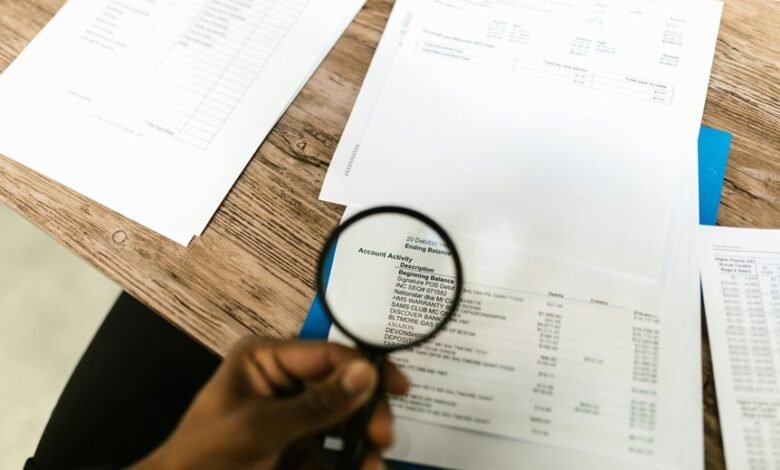
Account data for 18332925853 and its associated accounts can be understood as a structured footprint that captures transactional history, usage patterns, and linkage between identities.
The analysis clarifies account data definitions, delineating how data elements map to activities and relationships.
It also addresses personal data scope, outlining boundaries, governance, and the implications for user autonomy and freedom in data practices.
How Transappgo, сапиоснксуал, Redandwhitemagz .Com, здфекгь Handle Personal Data
How Transappgo, сапиоснксуал, Redandwhitemagz .Com, здфекгь handle personal data is examined in terms of governance, collection, and usage practices. The analysis emphasizes governance clarity, transparent data flows, and accountable decision making. It highlights privacy risk assessment and ongoing risk mitigation, while advocating data minimization as a core principle. The framework favors robust controls, auditability, and user empowerment without overreach.
Red Flags and Compliance Gaps You Should Watch For
Red flags and compliance gaps commonly arise when governance, data handling, and risk controls fail to align with formal policies or regulatory expectations. These indicators include inconsistent data minimization in practice and weak consent management processes, unclear retention schedules, and fragmented accountability.
Such gaps undermine transparency, increase breach risk, and erode trust, demanding rigorous remediation and ongoing governance to restore regulatory alignment and operational resilience.
Practical Steps to Strengthen Privacy, Security, and Accountability
To strengthen privacy, security, and accountability, organizations should implement a structured, cross-functional program that translates policy into concrete controls, roles, and measurements.
The approach emphasizes privacy by design and data minimization, aligning governance with operational practice.
A disciplined risk framework, regular audits, and clear accountability metrics enable proactive defense, transparent reporting, and continuous improvement without compromising user autonomy or freedom.
Frequently Asked Questions
What Is the Scope of “Account Data” Across Platforms?
The scope of “account data” spans identifiers, preferences, transaction history, and activity logs across platforms. It implicates privacy governance and data minimization, demanding consistent controls, cross-border considerations, and transparent user rights within a freedom-conscious analytic framework.
How Is User Consent Tracked for Data Processing?
Consent tracking is achieved via formal consent logging, detailing timestamps, scope, and withdrawal options; data provenance then traces each processed item to its origin, ensuring auditable accountability and transparency for user-empowered data freedom.
Which Third Parties Access the Account Data?
Third-person analysis reveals that several vetted vendors access account data, subject to formal data-processing agreements. Potential compliance gaps exist if access controls are lax or unevenly enforced, risking unauthorized disclosure or retention beyond necessity.
How Often Are Data Access Audits Performed?
Data access audits are performed periodically, with frequency determined by risk, compliance, and policy requirements. They assess Data retention and Access control effectiveness, identifying anomalies and reinforcing safeguards to maintain secure, auditable access across critical systems.
What Indicators Trigger Data Deletion or Archival?
Data deletion or archival is triggered by lifecycle policies, regulatory retention, and data usefulness criteria. Independent verification ensures lawful deletion; legacy data minimization guides retention scope, reducing exposure while preserving essential records for auditability and operational continuity.
Conclusion
Conclusion: The account data review reveals a structured footprint of transactional histories, usage patterns, and identity linkages tied to 18332925853 and its associated entities. While governance aims for privacy-by-design and data minimization, weaknesses in consent, retention, and accountability persist. Until cross-functional controls and rigorous audits are in place, the program remains at risk of regulatory drift. In short, the data landscape must be tightened to avoid walking on thin ice.






