Account Data Review – 185.63.253.290, 8554637258, Ofillmyzilla .Com, englishrebecca26xxx, 8334100241
The account data review for 185.63.253.290, 8554637258, Ofillmyzilla.com, englishrebecca26xxx, and 8334100241 adopts a structured health lens. It aggregates activity, engagement, and reliability metrics to identify stable login patterns and consistent feature use as indicators. Traces surface across services via standardized telemetry and unified identifiers to ensure traceability. Anomalies trigger validation, guiding evidence-based risk assessment and rapid remediation, all within privacy-by-design safeguards. The discussion pauses at a critical point, inviting further examination of containment and governance.
What the Data Points Tell Us About Account Health
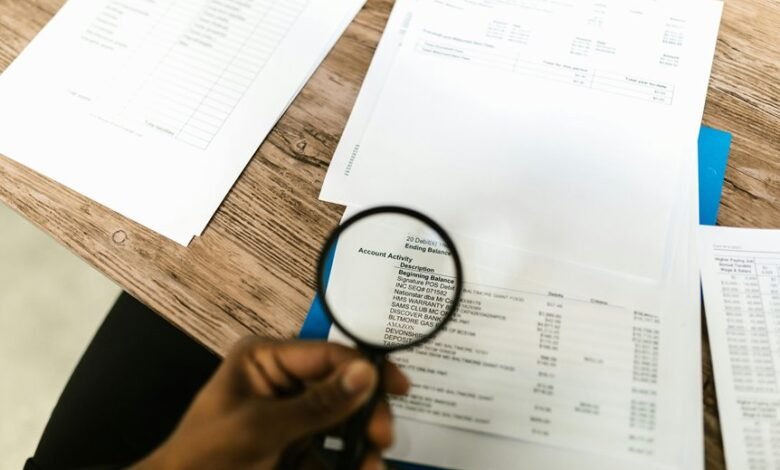
Data points reveal the overall health of the account by aggregating activity, engagement, and reliability metrics. The review isolates patterns without speculation, noting stable login frequency and consistent feature usage as indicators of account health. Data traces show correlations between timely interactions and outcome reliability, while anomalies trigger further validation. Conclusions remain neutral, emphasizing verifiability and accountability in ongoing monitoring.
How These Traces Surface Across Services and Why They Matter
How these traces surface across services is a function of standardized telemetry, cross-domain logging, and unified identifiers. They reveal patterns linked to account health and potential data exposure across platforms, enabling cross-checks and anomaly detection. The phenomenon underscores interoperability while preserving user autonomy; careful aggregation prevents noise, supporting investigations without sensationalism and guiding responsible data handling within a broader security-conscious ecosystem.
Detecting, Responding to, and Preventing Data Exposure Risks
Detecting, responding to, and preventing data exposure risks requires a structured, evidence-based approach that aligns monitoring, incident response, and proactive safeguards.
The analysis focuses on identifying anomalous access and data movements, correlating indicators across systems, and documenting severity.
Teams assess root causes, execute containment steps, and notify stakeholders.
Detecting risks informs rapid remediation, while preventing exposure relies on disciplined controls and continual validation.
Privacy, Compliance, and Practical Safeguards for Organizations
Privacy, compliance, and practical safeguards for organizations require a structured framework that aligns regulatory requirements with operational controls. The investigation highlights governance gaps, accountability lines, and policy enforcement while assessing privacy risks across data flows. Emphasis on data minimization reduces exposure, and rigorous access controls limit misuse. Transparent reporting, regular audits, and incident response readiness strengthen resilience and trust in compliant organizational practice.
Frequently Asked Questions
Which Laws Govern Handling This Specific Account Data Exposure?
The applicable laws vary by jurisdiction, but generally include data protection and privacy statutes, breach notification requirements, and sector-specific regulations; entities must ensure privacy compliance and robust access controls to mitigate exposure and secure personal information.
Can Data Points Indicate Insider Threats or Only External Attackers?
Data points can indicate both insider threats and external attackers; thus, a thorough risk assessment and data classification are essential to differentiate sources and inform defenses, rather than assuming one or the other. A watchful, methodical approach applies.
How Do False Positives Affect Incident Response Timelines?
False positives slow incident response timelines, diverting resources and delaying containment, while true threats persist; they complicate data exposure assessments, obscure insider threats, and compel repeated verification, reducing agility and risking degraded detection confidence in security operations.
What Are Cost-Effective, User-Friendly Remediation Steps?
Remediation prioritization favors affordable, user friendly tools that streamline incident timelines; threat indicators guide responses, while notifications privacy is preserved. Ironically, efficient remediation leverages transparent processes, objective metrics, and concise, actionable steps to empower users and minimize disruption.
How Is Customer Notification Managed Without Compromising Security?
Customer notifications are managed through formal security governance processes, ensuring timely, compliant alerts while preserving privacy; data minimization is applied to disclosures, reducing exposure. Communications favor transparency, non-punitive guidance, and verifiable incident handling adhering to governance standards.
Conclusion
From a detached, analytical vantage, the account traces cohere into a diagnostic mosaic: steady pulses reveal health; jagged spikes expose fault lines. Across services, standardized identifiers form a lattice—traceable yet restrained by privacy safeguards. Anomaly signals, when validated, become evidence-led catalysts for containment and remediation. The overarching lesson: reliable health hinges on minimal exposure, precise access controls, and timely, data-informed action, turning scattered telemetry into a disciplined, preventative practice rather than a reactive reflex.






